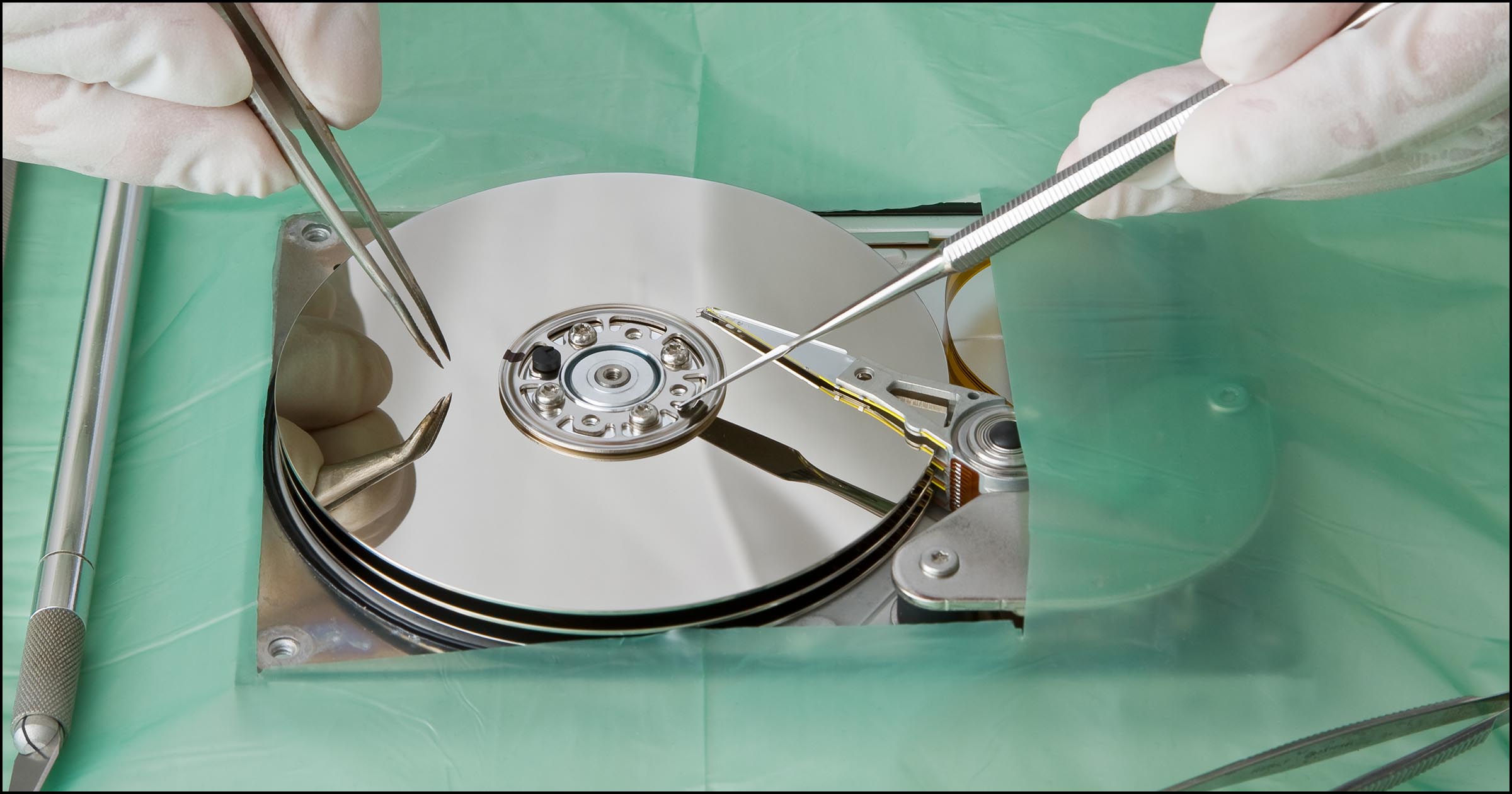
How To Data Recovery Files From Crypto locker For Free
Amazing news for anyone whose Data Recovery computer was affected by Crypto Locker! The long-awaited service for decrypting files held hostage by Crypto Locker is available. The solution comes shortly after Kyrus Technology researchers released a post with comprehensive details on how Crypto Locker works. Their post also contains information on how they impressively reverse engineered the process in order to obtain the key utilized to encrypt thousands of files.
Dell SecureWorks first discovered the Crypto Locker Trojan 3 years ago. Crypto Locker works by encrypting files, which have precise file extensions, and decrypting them once a ransom has been paid. Even though the network, which served the Trojan, was ultimately taken down, countless users remain Data Recovery separated from their files – until the way out was discovered. Are you a victim of Crypto Locker? Do you want to know how to get your files effortlessly back?

The Crypto Locker Trojan: Let’s Recap :
When Crypto Locker first burst into the scene, most tech nerds described it as the ‘nastiest malware of all time.’ Once the malware gets on your system, it seizes your files with a next-to-impossible to break Data Recovery encryption. What is more is that you will be charged a fortune to obtain your files back. The malware did not just attack local hard drives. It also harmed mapped network drive that is connected to an infected computer or an external hard drive. The attacks caused havoc in businesses where employees normally collaborate and share docs on a network attached storage drive (s).
How The Crypto locker Data Recovery Reversal Was Done :
After Kyrus Technologies successfully performed the Crypto Locker reverse engineering, the next thing they did was to create a decryption engine. Files that are encrypted with Crypto Locker malware normally follow a certain format but Every encrypted file is conducted using an AES-256 key, which is unique to the specific file. The information together with an understanding of file format utilized to store encrypted files enabled Kyrus Technologies to develop a highly effective decryption tool.
How To Decrypt Cryptolocker Infected Hard Drives :
The first thing you need to do is to visit decryptolocker.com. You will need a sample file that is encrypted with Crypto Locker malware to hand. After doing these two things, here are the steps you need to follow in order to recover files from Crypto Locker for free:
● Identify one Crypto Locker-encrypted document that you believe does not have sensitive Twitter Data Recovery. After finding it, upload it to crypto Locker portal. This service works perfectly on files that contain sensitive information.
● Be patient and you wait to receive a private key from the crypto Locker portal but You will also get a link where you can download and then install a decryption tool, that can operate locally on a computer.
● Run the decryption tool locally on your computer utilizing the private key provided. The process will decrypt all the encrypted files present in the hard drive.
Sadly, a number of new Crypto Locker variants continue to circulate. As much as they operate in the Data Recovery also same fashion to the Crypto Locker Trojan, a strategy to fix them is not yet available. The good news is that with technology, nothing is impossible. It is only a matter of time before an effective and long term solution becomes available.